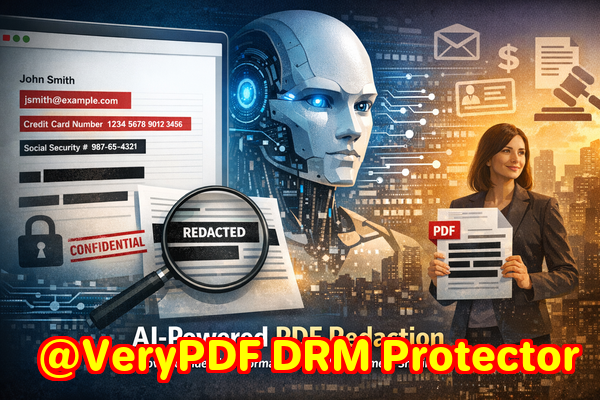
Securely Redact Sensitive Data in PDFs: Protect Confidential Information Offline
Last month, I sent a PDF contract to a business partner, only to realize later that it still contained unredacted client emails and financial details. The thought of accidentally violating GDPR or exposing confidential company data was terrifying. It was a stark reminder that even a small oversight in document handling can lead to massive compliance headaches, legal exposure, and reputational damage.
Many businesses underestimate the risks of sharing seemingly harmless PDFs. Whether it’s contracts, HR records, or financial reports, PDFs often contain sensitive information that, if not properly removed, can lead to fines, data breaches, or even legal action. Traditional redaction methodsblack boxes in Word, scribbles in PDFs, or online toolsrarely provide true security.
This is where AI-powered PDF redaction tools come into play, allowing professionals like us to permanently remove sensitive data while keeping everything offline and secure.
The Real Risks Businesses Face with PDFs
Accidental exposure of sensitive information is more common than most managers realize. Here are a few scenarios I’ve seen:
-
Hidden Personal Data in Shared PDFs: A marketing team shared a list of client contracts with a partner. Despite blacked-out text, a savvy user could copy and recover hidden names and emails. This created a GDPR compliance risk overnight.
-
Manual Redaction Errors: A finance department tried manually redacting salary details by highlighting and obscuring them. Later, it turned out the text was still searchable and copyablea nightmare waiting to happen during audits.
-
Unsafe Online Tools: Employees often turn to free online PDF redactors thinking it’s convenient. Unbeknownst to them, sensitive documents are uploaded to third-party servers, creating exposure to competitors or hackers.
Even one slip can cost thousands in fines, legal fees, or loss of client trust.
How AI PDF Redaction Solves These Problems
I discovered the VeryPDF AI PDF Redaction Tool Command Line, and it changed how we handle confidential documents. Here’s how it addresses the exact business risks:
-
Automatic Detection of Sensitive Data: The AI scans PDFs for names, emails, phone numbers, IDs, financial details, and legal clauses, flagging them instantly. There’s no need to hunt manually.
-
Permanent Removal, Not Just Hiding: Unlike traditional “black box” redactions, this tool completely removes sensitive information. Even sophisticated copy-and-paste or file recovery won’t reveal it.
-
Fully Offline Operation: Everything is processed on your local machine. Confidential files never touch the internet, eliminating third-party exposure risk entirely.
Imagine a legal firm preparing discovery documents. Instead of manually reviewing thousands of pages, the AI identifies all personal data, redacts it completely, and outputs a safe PDF ready to share. This eliminates human error and ensures compliance.
Practical Benefits You Can See
The impact of using a tool like this isn’t just theoretical. Here’s what we’ve observed:
-
Prevented Accidental Data Leaks: HR documents shared with external consultants were automatically cleaned, preventing sensitive employee data from being exposed.
-
Avoided Compliance Violations: One client avoided a GDPR penalty because all customer data in shared invoices was permanently redacted before sending.
-
Improved Employee Workflow: Switching from online tools to a local, AI-powered redaction solution made teams faster and more confident in document handling.
Step-by-Step Workflow for Secure PDF Redaction
To make this tangible, here’s a simple process we follow:
-
Load PDF Open the document you need to share.
-
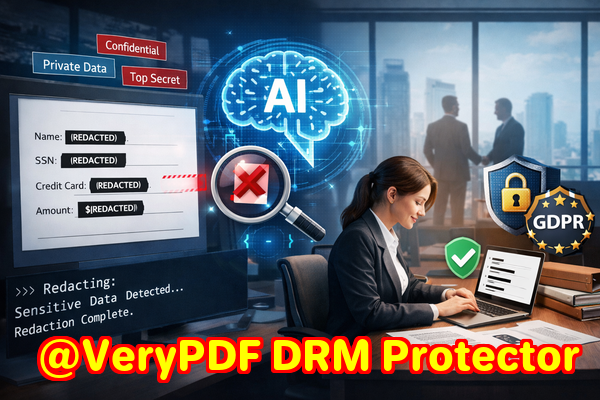
Detect Sensitive Data The AI scans for personal, financial, and confidential information.
-
Review Findings Confirm which items need redaction; adjust as needed.
-
Apply Redaction The tool permanently removes the sensitive data.
-
Export Clean PDF Share or store safely, knowing there’s no risk of recovery.
Common Types of Data to Redact
When using AI redaction, these are the most frequent categories we address:
-
Personal Identifiable Information (PII) Names, addresses, emails, phone numbers
-
Financial Data Bank details, invoices, salary information
-
Business Secrets Strategies, internal reports, sensitive meeting notes
-
Legal and Confidential Clauses Contracts, NDAs, settlement agreements
Real-World Examples
-
A law firm had to share hundreds of case files with opposing counsel. Using AI redaction, they removed all client identifiers offline, ensuring they met legal confidentiality requirements.
-
A healthcare provider needed to share patient summaries with insurance companies. The offline tool removed all patient PII, avoiding HIPAA violations and potential lawsuits.
-
A tech company was preparing a pitch deck with competitor data. AI redaction helped them redact internal strategic details before circulation, preventing leaks.
Why Offline Processing Matters
Online PDF redaction tools are convenient but risky. Sensitive documents uploaded to third-party servers are vulnerable to:
-
Cyberattacks and hacking
-
Employee negligence at the service provider
-
Compliance violations due to cross-border data storage
By keeping the process offline, VeryPDF ensures your documents never leave your environment, giving you complete control.
Conclusion
From my experience, permanently removing sensitive information from PDFs is not optionalit’s a business necessity. The VeryPDF AI PDF Redaction Tool Command Line automates detection, guarantees permanent removal, and keeps everything offline, solving real problems that managers, legal teams, and HR departments face daily.
I highly recommend this to anyone who needs to share documents safely without risking data leaks or compliance issues. Try it now and securely redact your PDFs: https://veryutils.com/smart-redact-server-ai-powered-pdf-redaction-software
Start your free trial today and ensure your sensitive data is permanently removed before sharing.
Frequently Asked Questions
-
How can I permanently remove sensitive data from a PDF instead of just hiding it?
Use AI-powered PDF redaction tools that remove data completely, rather than visually masking it.
-
Can others recover redacted information from my PDF?
With AI redaction, removed information cannot be recovered. Unlike blacked-out text, the data is deleted permanently.
-
Is it safe to use online PDF redaction tools?
Not entirely. Online tools upload documents to servers, which can create exposure and compliance risks.
-
Does this tool work completely offline?
Yes. VeryPDF AI PDF Redaction Tool processes everything on your local machine, ensuring total privacy.
-
What types of sensitive data can be automatically detected and removed?
Personal data (names, emails, IDs), financial information, legal clauses, business secrets, and other confidential content.
-
How can I ensure compliance with GDPR when sharing documents?
Permanently redact personal data before sharing. Offline AI redaction ensures no accidental exposure.
-
Can I review what will be redacted before applying it?
Yes. The tool allows reviewing detected sensitive data, giving you control before final redaction.
-
Is it suitable for large PDFs with thousands of pages?
Absolutely. AI automation makes it faster and more accurate than manual review.
-
Can I use it for internal and external document sharing?
Yes. It protects sensitive information for both internal teams and external partners.
-
Does it require technical expertise to use?
No. Even non-technical staff can follow a simple workflow to detect and redact sensitive data securely.
-
Can it detect sensitive data in multiple languages?
Yes. AI scanning can recognize and redact personal and confidential information in various languages.
Tags / Keywords
redact sensitive data, remove confidential information, PDF redaction tool, protect privacy in PDFs, prevent data leaks, offline PDF redaction, secure document sharing, AI PDF redaction, GDPR compliance, permanent data removal

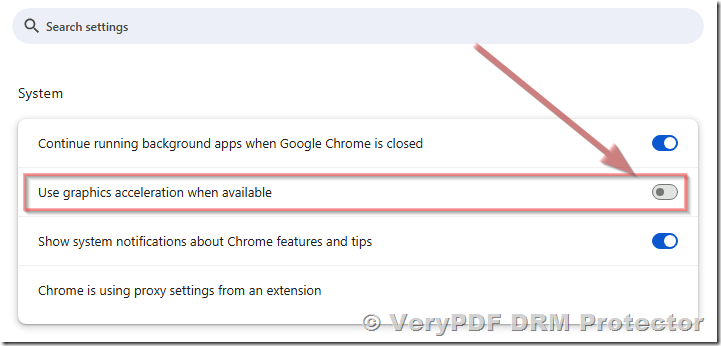 For Mozilla Firefox:
For Mozilla Firefox: