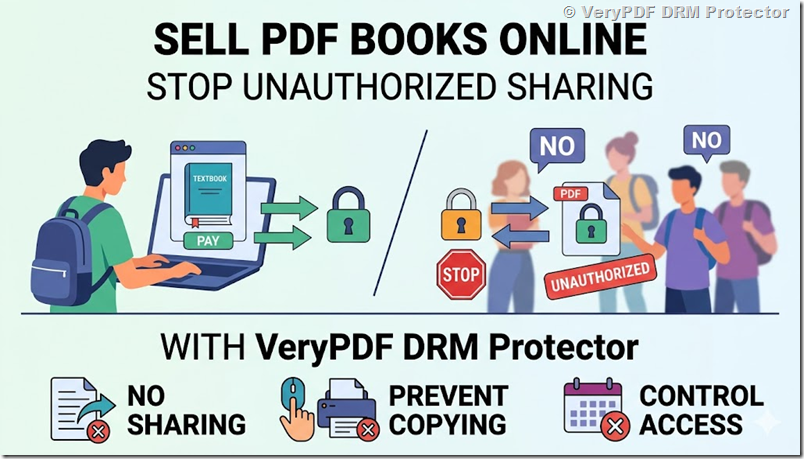
How to Sell a PDF Book Online and Stop Students Sharing It Without Permission
Recently, a retired military doctor contacted us with a question that many authors, professors, and educators are asking.
He wrote:
“I am writing a book on Community Medicine for undergraduate medical students. I want to publish it and monetize it with minimum investment. I am considering different options. Should I create my own website and distribute a secured PDF online? Or should I distribute the book offline using USB drives or other storage devices after protecting it? I would like to know the best options available.”
This is a great question.
Many authors spend months or years writing a book. After finishing the manuscript, they face a completely different challenge:
How do I sell my PDF book online and stop people from sharing it for free?
Medical professors are not the only people facing this problem.
The same issue affects:
- University professors
- Teachers
- Course creators
- Trainers
- Technical writers
- Research authors
- Educational publishers
They all want the same thing:
- Sell their content online
- Protect their intellectual property
- Prevent unauthorized sharing
- Keep costs low
- Stay in control of their content
The good news is that there is a practical solution.
Let’s look at the options available and see which one works best.
Should You Sell Your PDF Book Through Your Own Website?
In most cases, yes.
Creating your own website gives you full control over your business.
You control:
- Pricing
- Customer information
- Payments
- Promotions
- Updates
- Access permissions
Many successful authors create a simple website and sell their books directly to students.
After payment, students receive access to a protected PDF.
This approach avoids paying large commissions to third-party marketplaces and gives the author complete ownership of the customer relationship.
Why Ordinary PDF Passwords Are Not Enough
Many people think password-protected PDFs are secure.
Unfortunately, they are not.
Imagine this situation:
A student buys your textbook.
You send them the PDF and the password.
The student then forwards both the file and the password to ten friends.
Now eleven people have access even though only one person paid.
This is one of the biggest problems with ordinary PDF security.
Once the PDF leaves your computer, you lose control.
That is why many authors are moving to DRM-protected PDF files instead.
Why DRM Protection Is Better for Educational Books
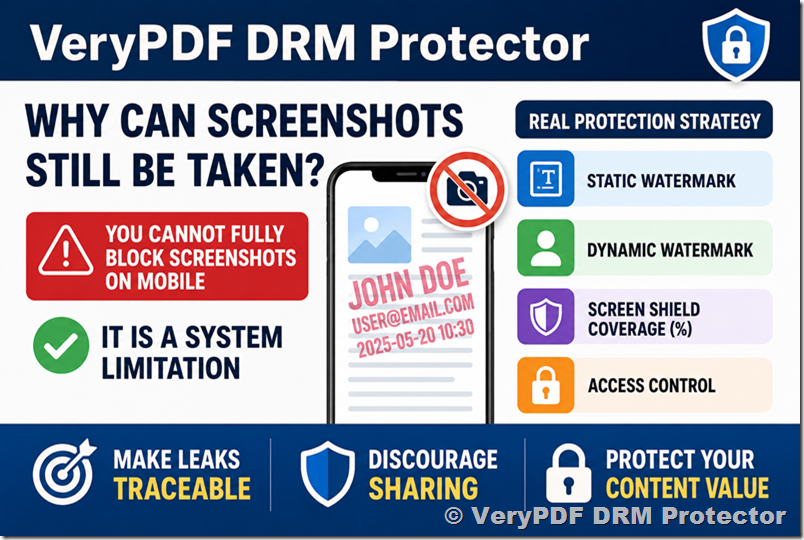
A DRM-protected PDF can provide much stronger protection than a simple password.
For example, you can:
- Prevent unauthorized sharing
- Prevent copying text
- Disable printing
- Add student-specific watermarks
- Set expiration dates
- Restrict access to authorized users
- Revoke access at any time
Even if someone shares the protected file, unauthorized users cannot simply open it.
This gives educators much greater control over their intellectual property.
Online Distribution vs USB Distribution
The doctor who contacted us also asked whether he should distribute his book through a website or use USB drives.
Technically, both methods work.
However, online distribution offers significant advantages.
Online Distribution
Advantages:
- Easy for students to access
- No shipping costs
- Instant delivery
- Easy updates
- Better security
- Ability to revoke access
- Ability to monitor usage
Disadvantages:
- Requires a website
USB Distribution
Advantages:
- Can work without internet access
Disadvantages:
- Shipping costs
- Hard to update content
- Difficult to monitor usage
- Difficult to revoke access
- Less convenient for students
For most authors, professors, and educators, online distribution is the better long-term solution.
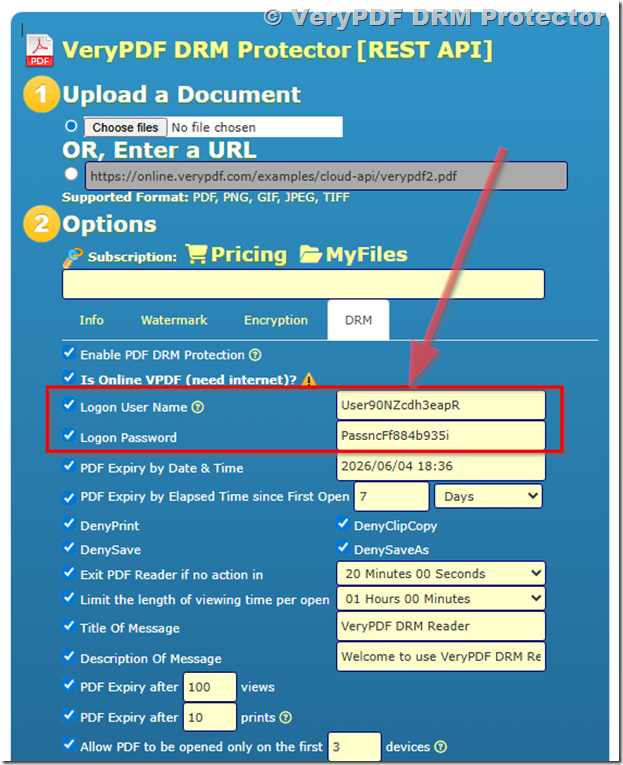
The Solution We Recommended
For the Community Medicine textbook author, we recommended a simple approach:
- Create a website.
- Protect the PDF using VeryPDF DRM Protector.
- Upload the protected PDF to the website.
- Sell access directly to students.
- Use DRM controls to prevent unauthorized sharing.
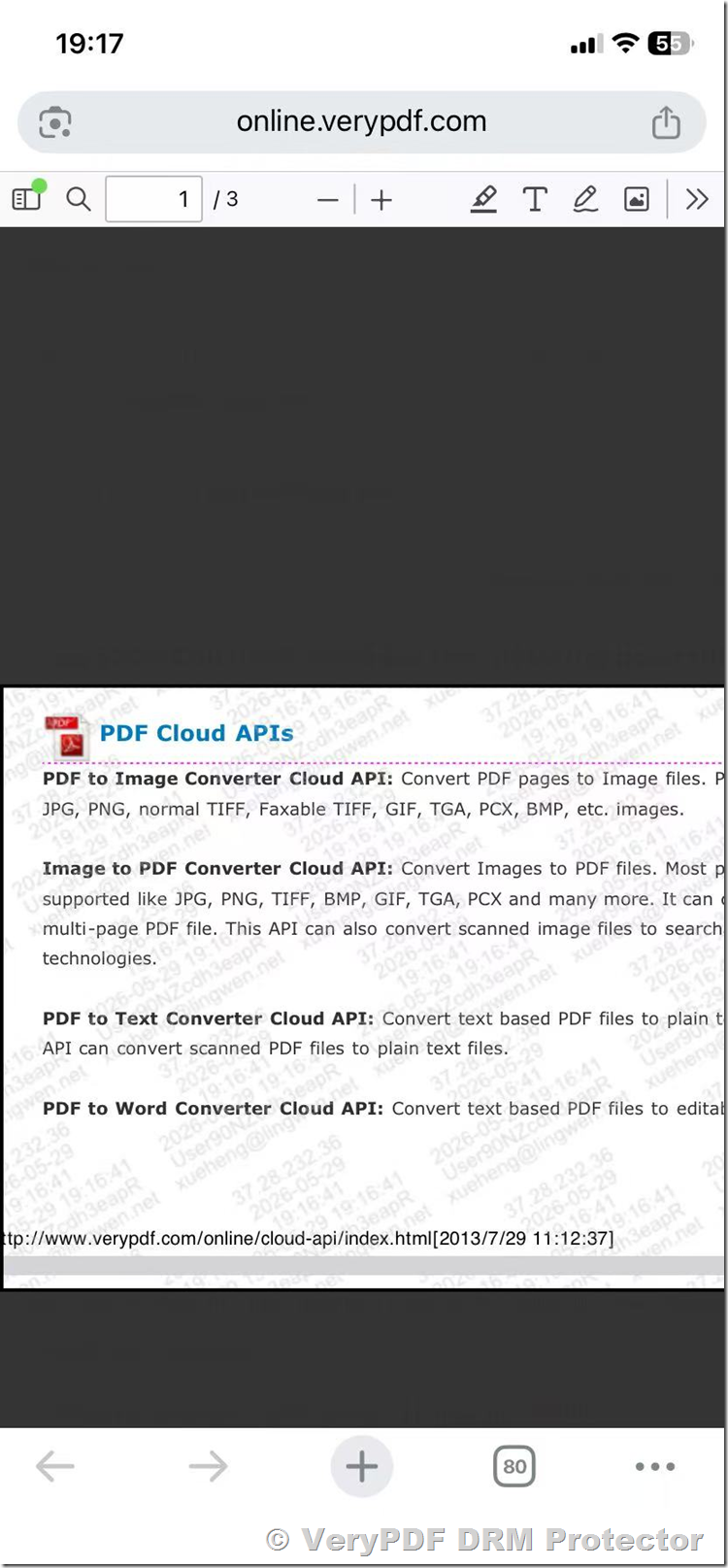
Students can remain on the author’s website and read the protected PDF online.
The DRM system handles user authentication and document protection, while the website handles sales and content delivery.
This combination provides strong security while keeping the process simple for students.
Can You Cancel Access Later?
Yes.
This is one of the biggest advantages of DRM protection.
Suppose a student requests a refund.
Or suppose unauthorized sharing is detected.
With DRM protection, access can be revoked without redistributing the document.
Traditional PDFs cannot do this.
Once an ordinary PDF is sent, there is usually no way to take it back.
Which VeryPDF Plan Is Best for Authors?
For most independent authors, professors, and educators, the Standard Plan is usually sufficient.
It includes the features needed to protect educational materials and sell PDF books online without a large upfront investment.
Learn more:
Purchase options:
https://drm.verypdf.com/purchase/
Final Thoughts
The retired doctor’s question is the same question thousands of authors ask every year:
“How can I sell my PDF book online without losing control of it?”
The answer is simple.
Use your own website for sales and use DRM protection to control access.
This gives you more security, more flexibility, and more control over your content than ordinary PDF passwords or offline USB distribution.
If you have spent months or years writing a book, protecting that work should be part of your publishing strategy from day one.

 What Is Dynamic Print Watermarking?
What Is Dynamic Print Watermarking?