Protecting Sensitive Data in PDFs: How Businesses Can Permanently Remove Confidential Information
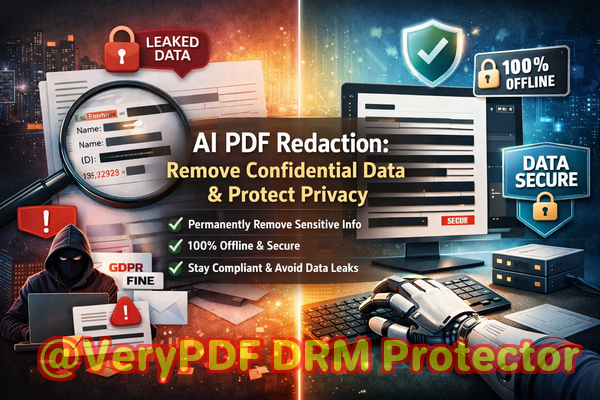
Last month, our legal team shared a PDF contract with a potential partner, only to realize later that it still contained unredacted employee personal data. The mistake could have resulted in a serious GDPR violation and reputational damage, not to mention the stress of scrambling to recall the document. For many businesses, this scenario is all too familiar: PDFs thought to be safe are leaking sensitive information, exposing organizations to compliance fines and legal risk.
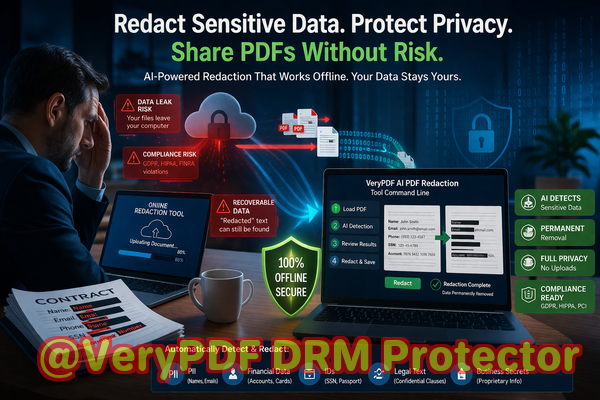
Accidental exposure of confidential information happens more often than companies realize. Whether it’s client details, employee records, or financial reports, the consequences can be severe. Manually redacting PDFs is time-consuming and error-prone. Employees may think they’ve “blacked out” sensitive information, only to have it still recoverable by copying text, OCR software, or even basic editing tools. Meanwhile, using free online redaction tools might seem convenient, but it introduces another risk: uploading sensitive data to unknown servers outside your control.
This is where VeryPDF AI PDF Redaction Tool Command Line becomes a game-changer. It offers businesses a reliable, offline solution to permanently remove confidential information, ensuring sensitive data never leaves your secure environment.
Many companies face recurring challenges when sharing PDFs. Here are some of the most common business pain points:
-
Accidental exposure of sensitive data: Names, emails, phone numbers, financial information, and other personal data often remain in shared PDFs. Regulatory frameworks like GDPR and HIPAA make these leaks not just embarrassing, but legally costly.
-
Ineffective manual redaction: Highlighting and blacking out text is risky. Digital traces of the original content often remain, meaning confidential information can still be extracted.
-
Unsafe online tools: Employees may turn to free web-based tools to redact PDFs, unintentionally uploading sensitive documents to third-party servers, which could lead to unauthorized access or leaks.
These challenges make it clear that businesses need a robust solution that ensures confidentiality without complicating workflows. VeryPDF AI PDF Redaction Tool Command Line addresses these problems effectively:
-
AI-powered detection: The tool automatically identifies sensitive data, including PII, financial data, phone numbers, email addresses, and even confidential clauses in contracts.
-
Permanent redaction: Unlike superficial “blackout” methods, it removes confidential information from the PDF entirely, making it unrecoverable.
-
Fully offline operation: All redaction processes happen on your local machine. There’s no risk of sensitive documents being uploaded to a server or cloud platform.
Consider a real-world scenario: a mid-sized consulting firm needed to share client reports with a partner. Previously, employees would manually redact the files, but small mistakes left client names exposed. After switching to VeryPDF AI PDF Redaction Tool Command Line, the firm could quickly process multiple reports, automatically removing all personal and financial data. This change not only ensured GDPR compliance but also gave staff confidence that sensitive information was safe.
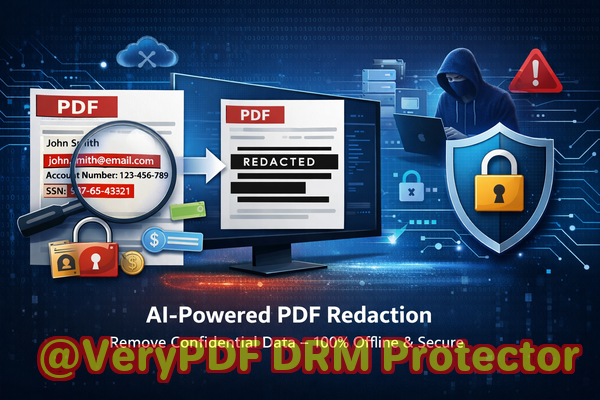
Another example comes from an HR department managing employee evaluations. Before using VeryPDF, they occasionally sent PDFs containing social security numbers and salary information to external auditors. With the offline redaction tool, the team now follows a simple workflow:
-
Load PDF Open the document in the command-line interface.
-
Detect sensitive data AI scans for names, emails, phone numbers, IDs, and financial information.
-
Review Quickly verify which elements need redaction.
-
Apply redaction Permanently remove all sensitive information.
-
Export clean PDF Share safely with auditors or partners, confident that the data is unrecoverable.
This workflow also works for a variety of data types, including:
-
Personally identifiable information (PII): Social security numbers, addresses, phone numbers, emails
-
Financial data: Bank account numbers, salaries, invoices
-
Business secrets: Internal strategies, project budgets, confidential contracts
-
Legal clauses: Proprietary agreements, non-disclosure agreements, sensitive legal notes
The advantages go beyond compliance. Companies using VeryPDF report:
-
Reduced risk of accidental data leaks, preventing fines or lawsuits.
-
Elimination of exposure from online tools, keeping all sensitive documents offline.
-
Increased employee efficiency, automating what was previously a time-consuming process.
For instance, a law firm handling client contracts moved from manual redaction to VeryPDF. Previously, staff spent hours verifying redactions, and errors occasionally slipped through. With the AI-powered tool, sensitive clauses were automatically detected and removed, freeing up legal teams to focus on casework rather than document cleanup.
Even small businesses benefit. A startup preparing investor reports needed to share financial projections while protecting trade secrets. Using VeryPDF, they ensured that confidential formulas and sensitive investor information were permanently removed from PDFs before distribution, preventing competitive exposure.
Using this tool is straightforward, even for non-technical staff. For example:
-
Load your PDF into the command-line interface.
-
Scan for sensitive content AI identifies what needs to be redacted.
-
Review redaction suggestions Approve or adjust as necessary.
-
Apply redaction Permanently remove the data.
-
Export and share The PDF is now safe to send to clients, auditors, or partners.
By integrating these steps into everyday workflows, businesses can prevent costly mistakes and protect both their reputation and legal compliance.
I highly recommend VeryPDF AI PDF Redaction Tool Command Line to anyone responsible for sharing documents containing sensitive information. The combination of AI-powered detection, permanent removal, and offline processing ensures that confidential data stays protected. It’s an essential tool for legal teams, HR departments, compliance officers, and any business handling sensitive PDFs.
Try it now and securely redact your PDFs: https://veryutils.com/smart-redact-server-ai-powered-pdf-redaction-software
Start your free trial today and ensure your sensitive data is permanently removed before sharing.
FAQs
1. How can I permanently remove sensitive data from a PDF instead of just hiding it?
Using VeryPDF AI PDF Redaction Tool, sensitive data is completely removed from the PDF, not just blacked out, making it unrecoverable.
2. Can others recover redacted information from my PDF?
No. The tool ensures redacted information is permanently deleted and cannot be restored or copied.
3. Is it safe to use online PDF redaction tools?
Online tools pose a risk because your files are uploaded to third-party servers, potentially exposing sensitive data. Offline solutions like VeryPDF eliminate this risk.
4. Does this tool work completely offline?
Yes. All processing happens locally on your computer, so confidential data never leaves your secure environment.
5. What types of sensitive data can be automatically detected and removed?
AI can detect and redact PII, financial data, legal clauses, phone numbers, emails, social security numbers, and business secrets.
6. How can I ensure compliance with GDPR when sharing documents?
By permanently redacting all personal data before sharing PDFs, you reduce the risk of accidental exposure and maintain GDPR compliance.
7. Can I use this tool for large batches of documents?
Yes. The command-line interface allows batch processing, making it efficient for businesses managing multiple PDFs.
8. Do I need technical skills to use the command-line version?
Basic familiarity with command-line operations is helpful, but the tool is designed to be user-friendly for business professionals.
9. How does AI detection improve redaction accuracy?
AI automatically identifies sensitive information that may be missed by manual redaction, reducing human error and improving compliance.
10. Can I review what will be redacted before applying changes?
Yes. The workflow allows you to review suggested redactions before permanently removing data.
11. Is this tool suitable for legal, HR, or financial documents?
Absolutely. It is ideal for contracts, employee records, financial reports, and any sensitive business documents.
12. What happens if I accidentally try to redact the wrong information?
You can review and adjust redaction suggestions before applying them, ensuring only the correct data is removed.
Tags/Keywords:
redact sensitive data, remove confidential information, PDF redaction tool, protect privacy in PDFs, prevent data leaks, offline PDF redaction, secure document sharing, GDPR compliance, AI PDF redaction, business document security