If you run an online learning platform, sooner or later you run into the same uncomfortable reality:
You upload premium course videos, students pay for access, and within days someone downloads, records, forwards, or reposts the content somewhere else.
At first, many developers assume basic video hosting or standard PDF-style password protection is enough. Then they discover how easily users can:
- record videos with OBS or Loom
- share login credentials
- download protected files through browser tools
- redistribute course materials privately
- bypass simple access restrictions
- leak confidential educational content
The problem becomes even more serious when your business depends on paid training, internal corporate education, certification programs, research materials, or proprietary intellectual property.

A common question developers ask is:
“Is there any real way to prevent screen recording of videos on an educational platform?”
The honest answer is:
No system can make screen capture mathematically impossible once content is visible on a user’s screen.
But there are practical ways to make unauthorized recording, downloading, forwarding, and redistribution significantly harder — hard enough that most users stop trying, and large-scale content leakage becomes much less common.
This article explains what actually works in real-world secure document sharing and secure video delivery systems, especially for platforms built with React and Node.js.
We’ll also look at why traditional password protection often fails, how DRM for PDF files and videos changes the security model, and how tools like VeryPDF DRM Protector help businesses maintain control over confidential digital content after distribution.
The Real Problem Is Not Just Screen Recording
Most developers initially focus on one thing:
“How do I stop OBS?”
But in practice, content leakage usually happens through multiple channels at once:
- browser downloads
- forwarded links
- shared accounts
- cached files
- copied text
- screenshots
- developer tools
- unauthorized cloud uploads
- internal employee leaks
- screen recording software
This is why secure document sharing and secure file sharing for business require layered protection rather than one single “anti-recording” feature.
For example, imagine a company selling premium certification courses.
Even if video downloads are disabled:
- users can still screen record
- PDFs can still be copied
- confidential training manuals can still be forwarded
- ex-employees may still retain access
- customers may share accounts internally
The issue is really about document access control and maintaining ownership over distributed content.
Why Traditional Password-Protected PDFs and Videos Fail
A lot of companies still rely on:
- password-protected PDFs
- private video URLs
- expiring links
- basic login systems
Unfortunately, these protections are weak in real-world environments.
Password-Protected PDFs Are Easily Shared
Once someone has the password, they can:
- send both the file and password to others
- upload the PDF elsewhere
- remove restrictions with third-party tools
- print or copy content
- store the document permanently
This is why many businesses searching for:
- PDF copy protection
- restrict PDF access
- share PDF without download
- protect confidential documents
eventually discover that passwords alone do not provide real control.
The Core Security Problem: You Lose Control After Distribution
This is the most important concept.
Traditional file sharing gives users a copy of the file.
Once they have the file:
- you cannot revoke access
- you cannot stop forwarding
- you cannot track redistribution
- you cannot control offline viewing
- you cannot prevent permanent retention
This applies to both PDFs and videos.
That’s why companies increasingly use DRM-based systems instead of standard file protection.
What DRM Actually Changes
DRM (Digital Rights Management) changes the security model from:
“Here’s a file.”
to:
“Here’s controlled access to content.”
That distinction matters.
Instead of giving users unrestricted ownership of files, DRM systems enforce rules such as:
- who can open content
- which device can access it
- whether downloading is allowed
- whether printing is allowed
- whether copying is allowed
- when access expires
- whether screenshots are blocked
- whether access can later be revoked
For educational platforms, this creates a much stronger foundation for secure document sharing and secure video delivery.
Can DRM Prevent Screen Recording Completely?
No.
No browser-based platform can guarantee absolute prevention.
However, modern DRM systems can make software-based recording substantially more difficult.
Depending on the platform and operating system, protections may include:
- blocking hardware acceleration capture
- protected video paths
- encrypted streaming
- disabling browser-level recording APIs
- watermarking
- screenshot blocking
- secure viewers
- controlled playback environments
Some desktop environments can also detect or interfere with common recording tools.
But the goal is deterrence and risk reduction — not absolute impossibility.
Browser Limitations Matter
If your platform runs entirely in a standard browser, your control is limited by the browser sandbox.
For example:
- browsers generally cannot detect all recording software
- JavaScript cannot reliably detect OBS
- users can bypass frontend restrictions
- screen capture APIs differ across operating systems
This is why many serious training providers move toward:
- DRM-enabled video streaming
- controlled desktop viewers
- protected PDF viewers
- device authorization systems
rather than relying entirely on browser logic.
What Actually Works in Real Educational Platforms
The most effective systems usually combine several protections together.
1. DRM-Protected Video Streaming
Instead of exposing raw MP4 files:
- videos are encrypted
- playback requires authorization
- streams are protected with DRM licenses
- direct downloads are restricted
This is commonly implemented using:
- Widevine
- PlayReady
- FairPlay
These help prevent simple downloading and casual redistribution.
However, DRM streaming alone does not fully solve screen recording.
2. Dynamic Watermarking
One of the most practical deterrents is visible watermarking.
For example:
- user email displayed on screen
- account ID overlaid dynamically
- timestamp watermarks
- IP-based identifiers
This dramatically reduces casual leaks because users know recordings can be traced back to them.
Many businesses find watermarking more effective in practice than aggressive blocking alone.
3. Restricting PDF Downloads and Forwarding
Educational platforms often include:
- training manuals
- worksheets
- certification documents
- confidential research PDFs
This creates another major leak vector.
Businesses searching for:
- prevent PDF download
- stop PDF forwarding
- lock PDF to specific users
- confidential document protection
usually discover they need more than password-protected PDFs.
A DRM-controlled PDF system can:
- prevent local saving
- stop copying
- disable printing
- lock access to specific devices
- revoke access remotely
- expire documents automatically
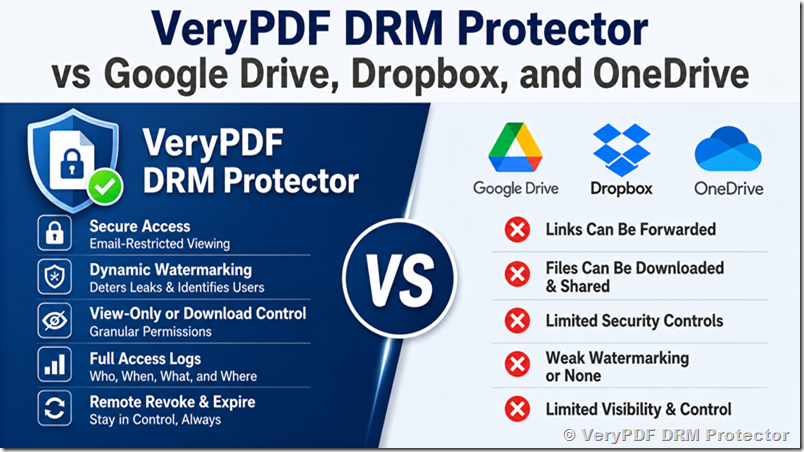
This is where solutions like VeryPDF DRM Protector are often used.
How VeryPDF DRM Protector Helps Control Distributed Documents
VeryPDF DRM Protector is designed for businesses that need stronger control over confidential PDFs, training materials, educational documents, and proprietary files.
Instead of relying on passwords, it applies DRM-based access control.
Some practical capabilities include:
- preventing PDF downloads
- restricting PDF access to authorized users
- stopping copy/paste
- disabling printing
- preventing forwarding
- setting expiration dates
- revoking access remotely
- locking files to specific devices
- tracking document usage
This is particularly useful for:
- online training companies
- coaching businesses
- certification providers
- internal corporate education
- legal documentation
- financial reports
- confidential research distribution
The important difference is that the organization retains control even after files are distributed.
Why Revocable Access Matters
One of the biggest frustrations businesses face is:
“Once I send the file, I lose control.”
For example:
- a contractor leaves the company
- a client relationship ends
- a subscription expires
- a student violates terms
- confidential materials leak
Traditional PDFs cannot realistically be recalled.
But DRM systems can revoke future access.
That capability becomes critical for secure document sharing in remote organizations.
Realistic Expectations About Screenshot and Screen Recording Prevention
This is where many companies get frustrated.
They search for:
- prevent screenshots or copying
- stop screen recording
- block OBS
- detect Loom
- disable screen capture
The reality is nuanced.
What You Can Do
You can:
- make recording harder
- reduce casual piracy
- block many software capture methods
- use protected playback paths
- watermark content
- monitor abnormal usage
- limit concurrent sessions
- restrict devices
- revoke access
- prevent downloads
What You Cannot Fully Guarantee
You cannot fully stop:
- external cameras
- modified operating systems
- advanced attackers
- virtual machines
- hardware capture devices
The goal should be:
- raising effort
- reducing convenience
- discouraging redistribution
- protecting commercial value
That’s how most successful educational platforms approach the problem.
Why Secure File Sharing for Business Requires Multiple Layers
A single protection method is rarely enough.
Strong systems combine:
- DRM
- watermarking
- user authentication
- device locking
- encrypted delivery
- access logging
- expiration controls
- restricted downloads
- viewer restrictions
This layered approach is far more effective than relying on:
- passwords alone
- hidden URLs
- frontend JavaScript protections
- disabled right-click menus
React + Node.js Integration Considerations
If your educational platform uses React and Node.js, you typically have several implementation paths.
Option 1: Browser-Based DRM Video Delivery
Pros:
- easiest deployment
- works across devices
- scalable
Cons:
- limited control over capture environments
- browser restrictions
Usually implemented using:
- encrypted HLS/DASH streaming
- DRM license servers
- authenticated playback tokens
Option 2: Secure Desktop Application
Some platforms move high-value content into:
- Electron apps
- native desktop applications
This enables:
- stronger playback control
- tighter OS integration
- better screenshot prevention
- more secure local environments
However:
- development complexity increases
- maintenance costs rise
- cross-platform testing becomes harder
Option 3: DRM-Protected Documents + Streaming
Many businesses separate:
- streaming video protection
- confidential document protection
For example:
- videos delivered through DRM streaming
- PDFs secured with DRM document protection
This layered architecture is common in:
- compliance training
- healthcare education
- financial certification
- enterprise learning systems
Why “No Download” Is So Important
A surprisingly common business concern is:
“I just want users to view the PDF without downloading it.”
This matters because downloaded files:
- persist forever
- can be re-uploaded
- can be redistributed endlessly
- bypass future policy changes
Businesses looking for:
- share PDF without download
- prevent PDF download
- secure PDF sharing
- PDF protection software
are usually trying to maintain long-term control over sensitive content.
This is exactly where DRM-based viewers are significantly stronger than ordinary PDF passwords.
Intellectual Property Theft Is a Real Business Problem
Many course creators underestimate how quickly valuable content spreads.
Examples include:
- premium courses reposted privately
- training manuals uploaded to forums
- internal documentation leaked externally
- certification materials shared among teams
- paid educational content redistributed through messaging apps
For smaller companies, this directly affects revenue.
For enterprises, it becomes a compliance and confidentiality issue.
This is why confidential document protection has become increasingly important for:
- SaaS businesses
- consulting firms
- legal organizations
- education providers
- healthcare companies
- corporate training teams
The Most Effective Mindset: Risk Reduction, Not Perfection
The companies that succeed with content protection usually avoid chasing “perfect prevention.”
Instead, they focus on:
- reducing unauthorized sharing
- discouraging casual abuse
- protecting commercial value
- maintaining access control
- minimizing leakage impact
This is a much more realistic operational strategy.
Even large streaming platforms cannot fully eliminate screen recording.
But they absolutely reduce piracy through layered security systems.
Educational platforms can apply the same principles at a smaller scale.
A Practical Security Stack for Educational Platforms
For most React + Node.js educational systems, a realistic modern setup might include:
Video Protection
- DRM streaming
- tokenized playback
- session expiration
- watermark overlays
- concurrent session limits
Document Protection
- DRM-secured PDFs
- restricted printing
- disabled copying
- device locking
- revocable access
User Controls
- MFA authentication
- device registration
- IP monitoring
- abnormal behavior detection
Administrative Controls
- access logs
- expiration policies
- remote revocation
- user-based permissions
This creates meaningful protection without pretending piracy can be eliminated completely.
Final Thoughts
If you are building an educational platform and wondering whether there is any real way to prevent screen recording, the honest answer is:
You cannot make screen capture impossible.
But you can make unauthorized downloading, forwarding, copying, and redistribution significantly harder through layered protection systems.
For most businesses, the real objective is not perfection — it is maintaining practical control over valuable content.
That means:
- secure PDF sharing
- document access control
- DRM-protected delivery
- restricted downloads
- revocable permissions
- watermarking
- controlled viewing environments
Traditional password-protected PDFs and simple video hosting rarely provide enough protection once confidential content is distributed.
Solutions like VeryPDF DRM Protector help organizations retain control over sensitive documents even after delivery, making them useful for companies handling proprietary training materials, paid educational content, confidential reports, and internal business documents.
If your platform already struggles with forwarded PDFs, leaked course materials, or uncontrolled file sharing, moving toward DRM-based protection is usually a far more effective long-term approach than relying on passwords or frontend restrictions alone.


 Protecting PDF and Document-Based Course Materials
Protecting PDF and Document-Based Course Materials