Protect, Share, and Track: A Complete Guide to Secure Document Management with VeryPDF DRM Protector
In today’s digital-first business environment, information is one of the most valuable assets an organization possesses. Whether it is financial reports, legal contracts, training materials, intellectual property, or internal communications, documents are constantly being created, shared, and stored across multiple devices and platforms. However, this convenience also introduces significant risks. Unauthorized sharing, data leaks, intellectual property theft, and uncontrolled distribution have become common challenges for businesses of all sizes.
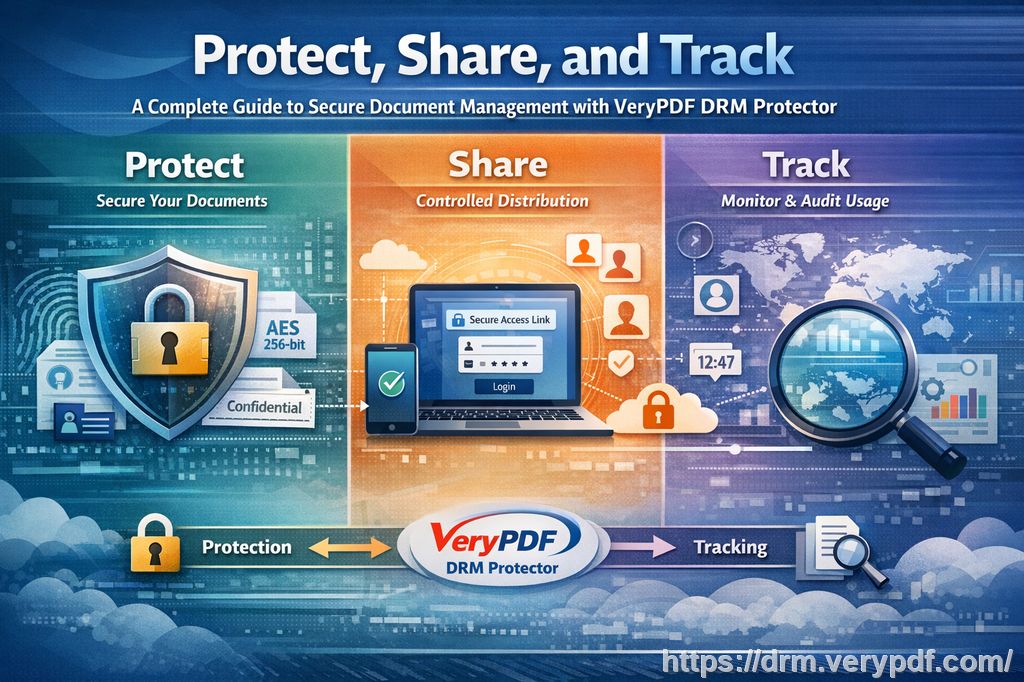
Traditional file protection methods such as password protection or basic encryption are no longer sufficient. Once a document is downloaded or shared, the originator often loses all control over it. This is where advanced Digital Rights Management (DRM) solutions become essential. VeryPDF DRM Protector is designed to address these challenges through a structured and powerful framework built around three core capabilities: Protect, Share, and Track.
These three pillars form a complete lifecycle of document security, enabling organizations not only to secure their files but also to control how they are used and gain visibility into their distribution. This article explores each of these features in detail and explains how they work together to solve real-world business problems.
1. Protect: Securing Documents at the Core
The foundation of any document security strategy is protection. Without strong protection, documents can easily be copied, modified, forwarded, or printed without permission. VeryPDF DRM Protector addresses this issue by applying enterprise-grade encryption and access control policies directly to the document.
At the heart of the Protect feature is 256-bit AES encryption, which ensures that files remain secure both in storage and during transmission. Unlike simple password protection, which can often be shared or cracked, encryption at this level ensures that only authorized users can access the content. Even if a file is intercepted or downloaded illegally, it remains unreadable without proper authorization.
However, encryption alone is not enough. VeryPDF DRM Protector goes further by embedding usage restrictions directly into the document. These restrictions allow document owners to define exactly how their content can be used. For example, they can control whether a document can be printed, copied, edited, or screen captured. They can also set expiration dates, limit access to specific devices, or restrict usage to certain geographic locations.
This level of granular control is particularly important for organizations dealing with sensitive or high-value content. Educational institutions can prevent students from distributing course materials outside of class. Corporations can ensure that internal financial reports remain confidential. Legal firms can protect contracts and case files from unauthorized duplication.
Another key aspect of protection is dynamic watermarking. Unlike static watermarks, dynamic watermarks automatically insert user-specific information such as email addresses, usernames, or timestamps into the document when it is opened. This acts as a strong deterrent against unauthorized sharing because any leaked copy can be traced back to the source user.
In essence, the Protect feature transforms a simple document into a controlled digital asset. It ensures that even after distribution, the creator retains full authority over how the document is accessed and used.
2. Share: Controlled and Secure Distribution
While protection is essential, documents are meant to be shared. The challenge lies in enabling secure sharing without losing control. Traditional methods such as email attachments or cloud links often result in uncontrolled distribution, where files can be forwarded endlessly without restriction.
The Share feature of VeryPDF DRM Protector solves this problem by introducing controlled distribution mechanisms. Instead of simply sending a file, document owners can distribute secure access links or license-based access permissions. This means that users do not receive unrestricted copies of the document; instead, they receive controlled access governed by predefined policies.
One of the most powerful aspects of this system is user authentication. Before accessing a document, users must verify their identity. This can be done through email authentication, account login, or integration with enterprise identity systems. Once authenticated, the system applies the appropriate permissions to that specific user.
This approach allows organizations to share documents confidently with employees, clients, partners, or students without worrying about unauthorized redistribution. Even if a link is forwarded, it will not work for unauthorized users.
In addition, sharing can be customized based on user roles. For example, a manager may have full access to edit and print a document, while a contractor may only have read-only access. This role-based control ensures that each user interacts with the document in a way that aligns with their responsibilities.
Another important feature is device control. Organizations can restrict document access to a limited number of devices, ensuring that content cannot be freely shared across multiple accounts or machines. This is especially useful in environments where sensitive data must remain within a controlled ecosystem.
The Share feature also integrates seamlessly with cloud environments, making it easy to distribute documents globally while maintaining strict control. Whether documents are accessed on desktops, tablets, or mobile devices, the same security policies apply consistently.
Ultimately, the Share capability transforms document distribution from an uncontrolled process into a secure, policy-driven system. It allows organizations to collaborate efficiently without compromising security.
3. Track: Visibility and Control Over Document Usage
One of the biggest limitations of traditional document security systems is the lack of visibility. Once a document is sent, the sender often has no idea how it is being used. Was it opened? Who accessed it? Was it shared further? Without answers to these questions, organizations cannot fully understand or control the lifecycle of their content.
The Track feature in VeryPDF DRM Protector addresses this gap by providing detailed analytics and usage monitoring for every protected document.
Every time a document is opened, accessed, or interacted with, the system records relevant data such as user identity, device type, location, access time, and actions performed within the document. This creates a complete audit trail that allows document owners to see exactly how their content is being used.
This level of tracking is particularly valuable in several scenarios. In corporate environments, managers can ensure that confidential reports are only accessed by authorized personnel. In educational settings, instructors can monitor student engagement with learning materials. In publishing and content distribution, authors can understand how widely their content is being accessed and by whom.
In addition to monitoring access, tracking also enables real-time control. If suspicious activity is detected, such as repeated unauthorized access attempts or unusual geographic logins, administrators can immediately revoke access or modify permissions. This dynamic control capability significantly reduces the risk of data leaks or misuse.
Another powerful aspect of tracking is compliance support. Many industries such as finance, healthcare, and legal services are required to maintain strict records of data access and usage. VeryPDF DRM Protector’s tracking system provides detailed logs that can be used for audits, compliance reporting, and internal investigations.
Furthermore, tracking data can be visualized through dashboards and reports, allowing organizations to gain insights into document performance and user behavior. This not only enhances security but also helps optimize content distribution strategies.
By combining visibility with control, the Track feature ensures that document security does not end at the point of distribution. Instead, it continues throughout the entire lifecycle of the document.
How Protect, Share, and Track Work Together
While each of the three features, Protect, Share, and Track, provides significant value on its own, their true power lies in how they work together as a unified system.
Protection ensures that documents are secure from the moment they are created. Sharing enables controlled and authenticated distribution without losing control. Tracking provides continuous visibility and enforcement throughout the document lifecycle.
Together, they create a complete DRM ecosystem that addresses every stage of document usage. This integrated approach eliminates the weaknesses of traditional security models, where protection ends once a file is delivered.
For example, a company can protect a confidential business proposal, securely share it with selected clients, and track how each client interacts with the document. If needed, access can be revoked instantly, even after distribution. This level of control is simply not possible with conventional document sharing methods.
Solving Real Business Pain Points
Organizations across industries face similar challenges when it comes to document security:
- Loss of intellectual property through unauthorized sharing
- Difficulty controlling access once documents are distributed
- Lack of visibility into how sensitive information is used
- Compliance risks due to insufficient audit trails
- Inefficient collaboration caused by overly restrictive security tools
VeryPDF DRM Protector directly addresses all of these issues by combining strong encryption, flexible access control, and real-time tracking into a single platform.
It allows businesses to protect their most valuable information without disrupting workflows. At the same time, it enables secure collaboration, ensuring that employees, partners, and customers can access the information they need, without exposing the organization to unnecessary risk.
Conclusion
In a world where digital information is constantly moving, copied, and shared, traditional document protection methods are no longer enough. Organizations need a smarter, more dynamic approach to security, one that evolves with how documents are actually used.
VeryPDF DRM Protector provides exactly that through its three core capabilities: Protect, Share, and Track. These features work together to ensure that documents remain secure, controlled, and visible throughout their entire lifecycle.
By implementing this solution, organizations can significantly reduce the risk of data leaks, protect intellectual property, improve compliance, and maintain full control over their digital assets, all while enabling seamless and secure collaboration.
In short, it transforms document security from a passive barrier into an active, intelligent system that empowers businesses to share information confidently and safely in the digital age.
