Ebook Piracy: How Can You Protect Your Ebook?
You may spend countless late nights outlining chapters, revising drafts, editing paragraphs, formatting pages, and preparing your ebook for readers. Publishing an ebook is often the result of months or years of dedication, creativity, and personal investment. When the book finally goes live, most authors feel proud, excited, and hopeful about reaching readers around the world.
Then comes a moment many authors never expect.
You search for your ebook title online, perhaps looking for reviews, blog mentions, or reader discussions, only to discover websites offering your ebook for free download. Sometimes the files are uploaded openly. Sometimes they are hidden behind suspicious subscription services. In other cases, unauthorized sellers are even making money from your work without your permission.
For many authors, discovering piracy feels personal. Your intellectual property, your time, and your income are suddenly exposed to strangers who believe digital content should simply be copied and distributed freely. The emotional frustration can be just as severe as the financial impact.
Ebook piracy has become one of the most persistent problems in digital publishing. Independent authors, educators, consultants, publishers, and businesses selling premium digital content all face the same challenge: once a digital file is distributed online, controlling it becomes difficult.
The good news is that ebook piracy can be reduced significantly when authors combine smart distribution practices, proper copyright management, monitoring tools, and strong DRM protection systems. Modern Digital Rights Management platforms now offer far more sophisticated protection than the simple password-based systems used years ago.
Among the most practical and professional solutions available for authors and publishers is VeryPDF DRM Protector, a dedicated ebook and document protection platform designed to prevent unauthorized sharing, copying, downloading, printing, and redistribution of digital content.
This guide explores how ebook piracy works, what kinds of risks authors face, why piracy continues to grow, and how professional DRM solutions like VeryPDF DRM Protector can help authors protect their work more effectively.
![[Solution] How to Protect Your Ebook from Piracy: Best DRM Solutions for Authors and Publishers [Solution] How to Protect Your Ebook from Piracy: Best DRM Solutions for Authors and Publishers](https://drm.verypdf.com/wp-content/uploads/2026/05/image-15.png)
What Is Ebook Piracy?
Ebook piracy occurs when an ebook is distributed, shared, copied, downloaded, or sold without the copyright holder’s permission.
Piracy can appear in several forms, and not all of them involve organized piracy websites. Sometimes the problem starts with ordinary readers who do not fully understand copyright restrictions.
Common examples include:
- A reader purchases your ebook and forwards the file to friends or colleagues.
- Someone uploads your ebook to a public file-sharing website.
- Torrent sites distribute copies of your book illegally.
- A third party sells your ebook through unauthorized marketplaces.
- Private online communities exchange copies of your ebook.
- Subscription piracy sites claim to offer unlimited access to your book collection.
- Social media groups share download links to your ebook.
Some piracy is intentional and commercial. Other piracy happens casually because digital files are easy to duplicate and share. Unfortunately, the end result is the same: your copyrighted material is being distributed outside your control.
For independent authors especially, this can create several serious concerns:
- Reduced ebook sales
- Lower perceived value of your work
- Loss of exclusive content control
- Unauthorized public exposure
- Damage to future launch performance
- Increased ranking of piracy sites in search engines
Authors who sell educational materials, technical documentation, premium reports, training manuals, or niche industry content may be even more vulnerable because their readers often purchase ebooks specifically for information value rather than entertainment.
Other Forms of Ebook Theft
Piracy is not the only threat authors face online.
Some individuals go beyond unauthorized sharing and directly steal content. They may repackage your material under a different name, modify sections of your text, or publish portions of your work as their own.
This falls into categories such as:
Copyright Infringement
This occurs when someone copies or distributes your protected work without authorization.
Plagiarism
Plagiarism involves taking portions of your writing and presenting them as original work without attribution.
Unauthorized Republishing
Some bad actors copy ebooks and upload them to marketplaces under fake publisher accounts.
Course and Membership Theft
Educational ebooks are often stolen and redistributed inside private learning communities or bundled into pirated online courses.
These issues can severely impact authors who rely on digital publishing revenue as part of their business model.
Why Ebook Piracy Is So Common
Digital publishing offers incredible convenience, but that convenience also creates vulnerabilities.
Unlike physical books, digital files can be copied instantly and distributed worldwide within seconds. Once an unprotected PDF or EPUB file is downloaded, it may spread rapidly across websites, cloud storage systems, forums, messaging apps, and social networks.
Several factors contribute to widespread ebook piracy:
Easy File Duplication
Digital files can be copied endlessly without quality loss.
Anonymous Sharing
Pirates often hide behind anonymous accounts, VPNs, or offshore hosting providers.
Global Distribution
Pirated files can spread internationally within hours.
Weak Protection Methods
Basic passwords and download restrictions are easily bypassed.
Reader Misunderstanding
Some readers genuinely believe sharing purchased ebooks with others is harmless.
Search Engine Visibility
Piracy sites frequently rank highly in search results for popular book titles.
The reality is that piracy cannot be eliminated completely, but strong protection systems can dramatically reduce unauthorized distribution and discourage casual sharing.
Understanding DRM (Digital Rights Management)
Digital Rights Management, commonly called DRM, refers to technologies that control how digital content is accessed, copied, shared, printed, or distributed.
DRM systems are designed to protect ebooks and other digital files by limiting what users can do with them after purchase.
For example, DRM may allow readers to:
- Read an ebook on approved devices
- Access content only after authentication
- View files online without downloading them
At the same time, DRM can prevent users from:
- Copying text
- Printing pages
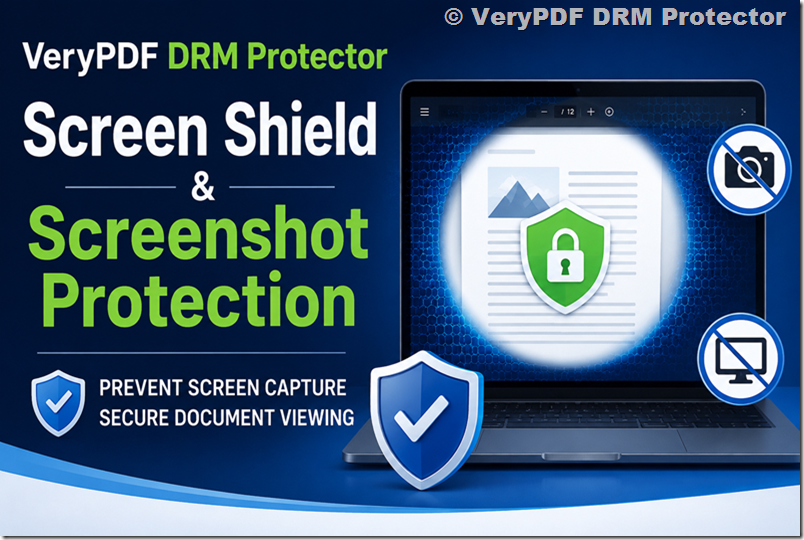
- Taking screenshots
- Sharing files with others
- Downloading raw PDF files
- Accessing content after subscription expiration
Traditional DRM systems have existed for years, but many older systems were inconvenient for legitimate readers and often failed to stop determined pirates.
Modern DRM platforms are far more advanced. Professional solutions like VeryPDF DRM Protector combine encryption, device authorization, dynamic watermarking, browser-based viewing, access expiration, and anti-copy controls into a unified protection system.
The Limitations of Traditional DRM
Although DRM can be highly effective, older DRM systems developed a bad reputation because they sometimes created frustrating user experiences.
Readers occasionally encountered problems such as:
- Device compatibility issues
- Complex activation steps
- Restricted offline access
- Inability to transfer books between devices
- Confusing authentication requirements
Some organizations and readers criticized DRM because legitimate customers sometimes experienced more inconvenience than pirates.
At the same time, no DRM solution is absolutely impossible to bypass. A determined individual could theoretically photograph pages, manually retype content, or capture screenshots.
However, modern DRM does not aim to achieve impossible perfection. Instead, the goal is to:
- Prevent mass casual sharing
- Discourage unauthorized redistribution
- Increase the effort required for piracy
- Trace leaks through watermarking
- Protect commercial value
- Reduce large-scale content theft
This is where enterprise-grade solutions such as VeryPDF DRM Protector become especially valuable.
Why VeryPDF DRM Protector Is Different
VeryPDF DRM Protector is designed specifically for protecting sensitive PDF documents, ebooks, educational materials, training manuals, research reports, and premium digital publications.
Unlike simple password-protected PDFs, the platform applies professional-grade DRM controls that remain active even after the file is delivered to readers.
The system helps authors and publishers maintain control over how their ebooks are accessed and used.
Key capabilities include:
Strong PDF Encryption
VeryPDF DRM Protector encrypts your ebook files to prevent unauthorized access and redistribution.
Prevent Downloading
You can allow readers to view ebooks securely in a browser without giving them downloadable source files.
Stop Copying and Printing
The platform can block copying, printing, editing, and screen grabbing attempts.
Device Locking
You can limit ebook access to authorized devices only.
Expiration Controls
Authors can set expiry dates or usage limits for ebook access.
Dynamic Watermarking
Visible watermarks containing reader information discourage file sharing and help identify leaks.
Access Revocation
If necessary, access to an ebook can be revoked remotely even after distribution.
Browser-Based Secure Reading
Readers can access protected content through secure environments without needing complicated software installations.
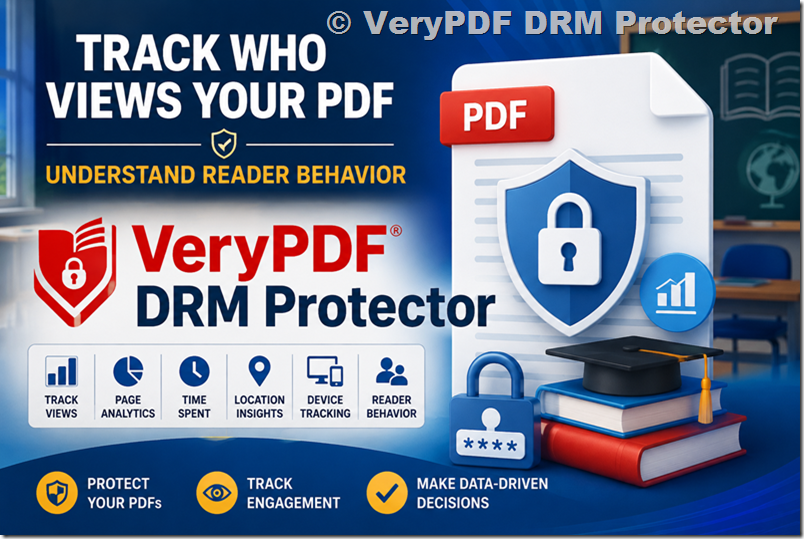
Analytics and Tracking
Publishers can monitor usage activity and access patterns.
For authors selling premium ebooks, online courses, confidential reports, or membership content, these protections provide a much higher level of security than standard ebook delivery methods.
Social DRM and Watermarking
One effective anti-piracy strategy is Social DRM.
Instead of aggressively restricting readers, Social DRM adds identifying information directly into the ebook itself. This may include:
- Buyer name
- Email address
- Purchase ID
- Transaction date
- Custom watermark text
The idea behind Social DRM is psychological deterrence. Readers are less likely to upload a file publicly when their personal information is embedded visibly or invisibly inside the document.
VeryPDF DRM Protector supports watermarking technologies that can help discourage unauthorized sharing while maintaining a smooth reading experience for legitimate customers.
This approach works especially well for:
- Business reports
- Educational content
- Internal training manuals
- Professional ebooks
- High-value technical publications
Unlike traditional password systems, watermarking does not interfere heavily with usability while still adding accountability.
How Limiting Downloads Helps Protect Ebooks
Another practical protection strategy involves controlling download access.
Unlimited downloads create opportunities for users to share download links publicly or distribute files across multiple unauthorized users.
A smarter approach is to:
- Limit the number of downloads per customer
- Restrict simultaneous device usage
- Require account authentication
- Monitor suspicious access patterns
Professional DRM systems like VeryPDF DRM Protector allow publishers to configure detailed access permissions while still supporting legitimate readers who need access across personal devices.
This balance between usability and security is extremely important because overly restrictive systems can frustrate paying customers.
What to Do If Your Ebook Is Pirated
Discovering piracy can feel overwhelming, but there are several practical steps authors can take.
Contact the Website Owner
Some smaller websites will remove content voluntarily after receiving a copyright complaint.
Issue DMCA Takedown Notices
The Digital Millennium Copyright Act (DMCA) allows copyright owners to request removal of infringing content from hosting providers and search engines.
A proper DMCA notice generally includes:
- Your contact information
- Proof of ownership
- The infringing URL
- A statement of good faith
- A request for removal
Contact Search Engines
Google allows copyright holders to submit removal requests for pirated search results.
Monitor Repeat Offenders
Some piracy sites re-upload content repeatedly, so ongoing monitoring may be necessary.
Improve Protection Going Forward
If your ebook spreads widely after release, stronger DRM protection should become part of your publishing workflow.
Using advanced protection before distribution is significantly easier than trying to remove thousands of unauthorized copies later.
How to Detect Ebook Piracy
Many authors only discover piracy accidentally.
Monitoring your content regularly helps identify problems earlier.
Search Your Ebook Title
Search Google using:
- Your book title
- Your author name
- Keywords like “download PDF”
- Keywords like “free ebook”
Be cautious when visiting suspicious websites because many piracy platforms contain malware, deceptive ads, or phishing schemes.
Set Up Google Alerts
Google Alerts can notify you whenever your ebook title or author name appears online.
Use Mention Monitoring Tools
Services such as Mention.com track online references across websites and social platforms.
Monitor Search Rankings
If piracy websites begin ranking prominently for your ebook title, stronger enforcement may become necessary.
Does Copyright Automatically Protect Your Ebook?
In most countries, yes.
Your ebook is automatically protected by copyright as soon as it is created in tangible form.
You generally do not need to file formal registration to own copyright protection, although registration may strengthen legal enforcement in certain jurisdictions.
Adding a copyright notice to your ebook is still recommended because it:
- Clarifies ownership
- Discourages casual copying
- Establishes professional publishing standards
However, copyright alone does not physically stop piracy. That is why technical protection systems like DRM remain important.
Are Piracy Sites Really Hosting Your Ebook?
Interestingly, many piracy sites claiming to offer ebook downloads do not actually possess the files.
Instead, they may:
- Trick users into purchasing fake subscriptions
- Spread malware
- Collect email addresses
- Redirect visitors through advertising scams
Still, many major piracy platforms do host real ebook files, especially for bestselling or educational content.
Authors should not assume listings are harmless simply because some sites are fake.
Is Fighting Piracy Worth Your Time?
The answer depends heavily on your situation.
For new authors with limited visibility, piracy may not significantly affect sales. Lack of exposure is often a bigger challenge than unauthorized copying.
Many independent authors choose to focus their energy on:
- Marketing
- Audience building
- Publishing additional books
- Improving discoverability
- Expanding reader engagement
However, established authors, educators, consultants, and professional publishers may experience measurable financial losses from piracy.
If piracy sites dominate search results or large-scale redistribution becomes widespread, taking action becomes much more important.
In those situations, combining legal enforcement with strong DRM protection provides the best long-term strategy.
Cases Where Piracy Can Seriously Harm Sales
Some authors report clear financial damage linked to piracy.
When pirated versions become easier to find than legitimate purchase pages, potential customers may simply download unauthorized copies instead of buying.
This problem becomes especially severe for:
- Textbooks
- Professional training content
- Certification guides
- Technical manuals
- Premium research reports
- High-demand fiction series
Authors who release sequels or subscription-based content may also experience declining sales if earlier books spread widely through piracy channels.
The larger your audience becomes, the more important content protection tends to become.
Why Prevention Is Better Than Cleanup
Many authors only think about DRM after piracy occurs.
Unfortunately, once a clean PDF spreads online, removing every copy becomes nearly impossible.
That is why prevention matters.
Using a professional protection system before distribution allows authors to:
- Control file access from the beginning
- Prevent uncontrolled downloading
- Deter casual sharing
- Track suspicious activity
- Reduce redistribution risks
- Maintain stronger content ownership
This proactive approach is particularly important for authors building long-term digital publishing businesses.
How VeryPDF DRM Protector Helps Ebook Authors
VeryPDF DRM Protector offers a practical and professional solution for authors who want stronger control over their digital publications.
The platform is especially useful for:
- Independent ebook authors
- Educational publishers
- Online course creators
- Membership businesses
- Corporate trainers
- Technical writers
- Research organizations
The system protects PDF ebooks using advanced DRM controls that go far beyond ordinary password security.
Authors can decide exactly how readers interact with their content.
For example, you can:
- Allow online viewing only
- Prevent file downloads
- Block copying and printing
- Limit device access
- Add personalized watermarks
- Set expiration dates
- Revoke access remotely
These features help reduce the most common forms of ebook piracy while preserving a professional reading experience.
Another important advantage is flexibility. Different ebooks require different protection levels. A free lead magnet may need only watermarking, while a premium training manual may require strict viewing restrictions and device authorization.
VeryPDF DRM Protector allows publishers to configure security based on their business model and audience requirements.
Balancing Security and Reader Experience
One mistake some publishers make is prioritizing security so aggressively that legitimate customers become frustrated.
Good DRM should not punish paying readers.
The best protection systems balance:
- Security
- Convenience
- Accessibility
- Device compatibility
- Ease of reading
Modern browser-based DRM platforms help simplify access while maintaining strong protection.
Readers should be able to purchase and read ebooks smoothly without complicated technical steps, while authors retain meaningful control over distribution.
This balance is one reason professional DRM platforms continue evolving beyond older ebook protection methods.
Should New Authors Worry About Piracy?
For most first-time authors, obscurity is usually a bigger concern than piracy.
People cannot pirate books they do not know exist.
Many independent authors initially benefit more from focusing on:
- Building an audience
- Collecting reviews
- Growing email lists
- Improving discoverability
- Publishing consistently
However, authors selling premium educational or business content should think about protection earlier because their materials often attract commercial piracy much faster.
If your ebook contains valuable information people would normally pay substantial money to access, DRM protection becomes much more important.
Final Thoughts
Ebook piracy is an unfortunate reality of digital publishing. Whether you are an independent novelist, a technical writer, a coach, an educator, or a professional publisher, your content may eventually appear on unauthorized websites.
Completely eliminating piracy is unrealistic, but reducing it significantly is absolutely possible.
The most effective strategy combines several elements:
- Strong DRM protection
- Watermarking
- Controlled downloads
- Monitoring tools
- DMCA enforcement
- Search monitoring
- Smart distribution practices
For authors serious about protecting their digital products, relying on simple passwords or unprotected PDFs is no longer enough.
Professional DRM systems like VeryPDF DRM Protector provide a far stronger layer of security by controlling how ebooks are viewed, copied, printed, shared, and distributed.
Protecting your ebook does not mean distrusting your readers. It means protecting the value of your work, your business, and the time you invested creating something meaningful.

![[Solution] Preventing Screenshot on Mobile Devices (iOS & Android): Why It Is Impossible on Web and What the Real Enterprise-Grade Solution Looks Like [Solution] Preventing Screenshot on Mobile Devices (iOS & Android): Why It Is Impossible on Web and What the Real Enterprise-Grade Solution Looks Like](https://drm.verypdf.com/wp-content/uploads/2026/05/image-16.png)
![[Solution] How to Protect Your Ebook from Piracy: Best DRM Solutions for Authors and Publishers [Solution] How to Protect Your Ebook from Piracy: Best DRM Solutions for Authors and Publishers](https://drm.verypdf.com/wp-content/uploads/2026/05/image-15.png)
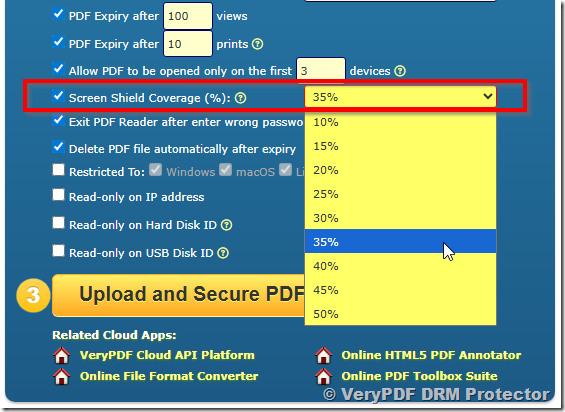 Step 3
Step 3