In today’s fast-paced digital environment, sharing documents securely has become more critical than ever. Sensitive files, whether PDF, Office documents, images, video, or audio, often need to be shared with clients, colleagues, or students, but traditional file-sharing solutions can leave your content exposed once a download occurs. VeryPDF DRM Protector addresses this challenge with its Persistent Protection After Download (PPAD) feature, enabling users to maintain complete control, track engagement, and enforce security even after files leave your system.
What is PPAD?
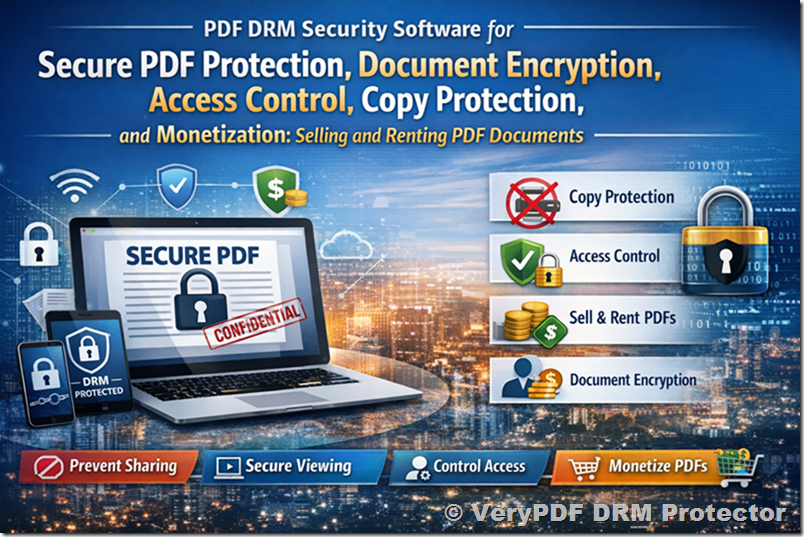
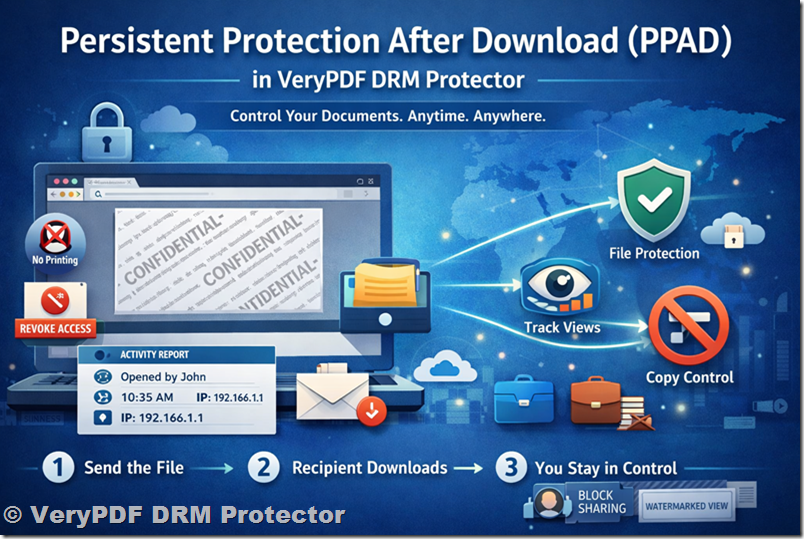
Persistent Protection After Download (PPAD) is a patent-pending Digital Rights Management (DRM) technology developed by VeryPDF. Unlike traditional DRM tools or Virtual Data Rooms (VDRs), PPAD ensures that your files remain secure and under your control even after the recipient downloads them. With PPAD, your sensitive documents don’t stop being protected once they leave your platform, they carry their security with them, everywhere.
PPAD combines access restrictions, copy controls, watermarking, and engagement tracking into a single, easy-to-use solution. Whether you’re sharing a single file, a full folder, or a secure data room, PPAD keeps your content safe and allows you to monitor every interaction with your files.
How PPAD Works: Simple, Transparent, Secure
Using PPAD is straightforward and requires no additional software for your recipients. The process follows three simple steps:
- You send the file
Upload your document to VeryPDF DRM Protector and apply your security settings. Decide who can access the file, which devices can open it, and what restrictions to apply. - Recipient downloads PPAD-protected file
The file can be downloaded directly in the browser, or via your secure data room, cloud storage, or even through an integrated API in your own applications. - You stay in control
Even after download, you can:- Revoke access at any time
- Block printing and sharing
- Watermark every view
- Track who opens it, when, and for how long
This approach ensures that you never lose control of your documents, no matter where they go or who has them.
Features That Make PPAD Stand Out
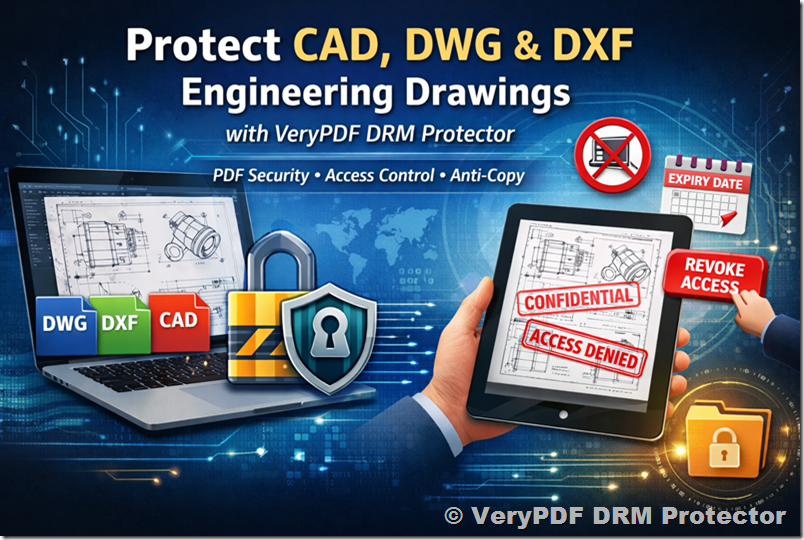
1. Protect Files Everywhere
Most secure file-sharing services lose control once a file is downloaded. PPAD ensures protection travels with the file, making sure your rules—expiry dates, watermarks, and usage limits—remain active even offline. Recipients can work without an internet connection after initial access, while your control settings remain intact.
2. Browser-Only Access
PPAD does not require a desktop app. Files open directly in the browser, giving recipients a seamless experience while keeping your content secure.
3. Multi-Format Support
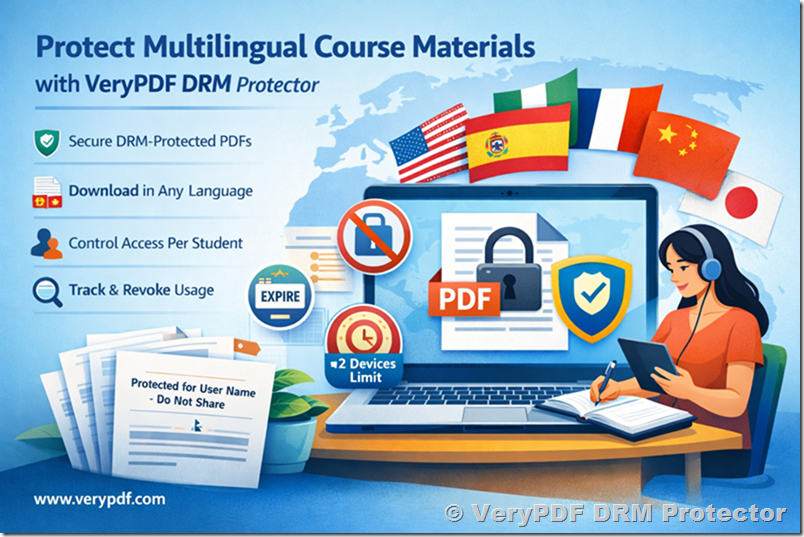
PPAD supports a variety of formats, including:
- Microsoft Office documents (Word, Excel, PowerPoint)
- Images
- Video and audio files
This flexibility allows you to protect all kinds of sensitive content with a single solution.
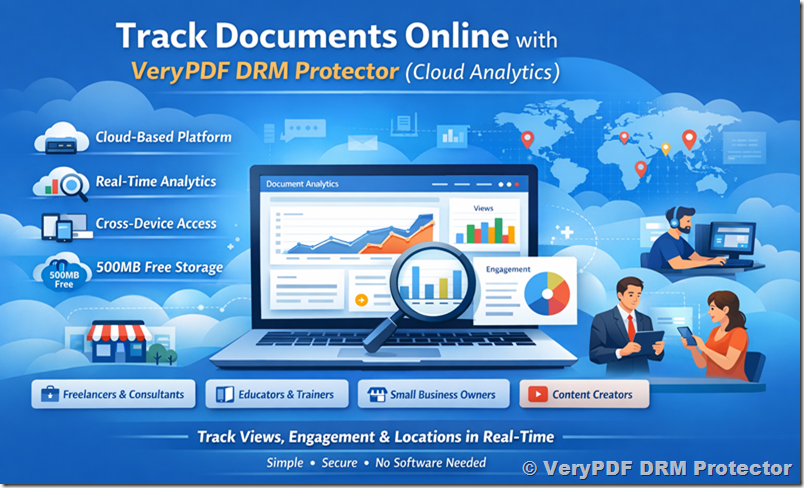
4. Page-by-Page Tracking
Understand how recipients engage with your content with detailed insights. Track every page view, download, or interaction, giving you the ability to measure engagement and identify who accessed your files.
5. Integration with Cloud Storage and APIs
Use PPAD directly in VeryPDF DRM Protector’s secure file sharing and data rooms, or integrate it with your existing cloud storage platforms, including SharePoint, OneDrive, Google Drive, Box, or Dropbox. For businesses and developers, PPAD can also be embedded via API into custom workflows and applications, available as an on-premise solution.
PPAD vs Traditional DRM and VDR Tools
|
Feature |
VeryPDF DRM Protector PPAD |
Traditional DRM / VDR |
|
Desktop App Required |
❌/✅ Supported in both browser and desktop |
✅ Often required |
|
Works After Download |
✅ Yes |
❌ Usually not |
|
Multi-Format Support |
✅ PDF, Office, images, video, audio |
❌ Limited |
|
Page-by-Page Tracking |
✅ Yes |
❌ Rarely |
|
Offline Access |
✅ Yes, controlled |
❌ Limited |
|
Revoke Access Anytime |
✅ Yes |
❌ Sometimes difficult |
PPAD eliminates the limitations of traditional solutions, offering a faster, easier, and more reliable way to protect files after download.
Use Cases for PPAD
Secure Document Sharing
Send a single file or multiple documents to recipients while preventing unauthorized copying, sharing, or printing. Every view is tracked, so you know exactly who accessed your content.
Virtual Data Rooms (VDR)
Share entire folders securely with access control, Q&A functionality, and audit logs. PPAD ensures files remain protected even after download, making it ideal for sensitive business transactions or internal reporting.
Education and Training
Teachers, instructors, and training organizations can distribute course materials while retaining control over content. Prevent redistribution of proprietary teaching resources and track student engagement effortlessly.
Enterprise Workflows
Integrate PPAD into your enterprise applications via API, maintaining document security across internal and external workflows. Keep control over sensitive reports, legal contracts, or financial documents even after distribution.
Security That Stays With Your File
Persistent Protection After Download ensures your security travels with the document:
- Built-in Protection: Files remain secure even if copied, forwarded, or shared.
- Your Rules, Everywhere: Expiry dates, watermarking, and usage limits stay active.
- Offline Ready: Recipients can work offline without losing your control.
With ISO27001 certification and a patent-pending DRM system, PPAD is designed to provide control, convenience, and compliance for individuals and businesses alike.
Why Choose VeryPDF DRM Protector PPAD?
- Control Beyond the Cloud: Traditional VDRs or secure sharing solutions stop protecting files after download, PPAD continues protection anywhere.
- No Desktop App Hassle: Works entirely in the browser, on any device.
- Flexible Deployment: Available in VeryPDF DRM Protector, cloud storage, and via API integration.
- Comprehensive Tracking: Detailed page-by-page engagement insights.
- Multi-Format Support: PDF, Office, images, audio, and video, all protected with the same system.
With PPAD, VeryPDF DRM Protector makes digital rights management simple, effective, and persistent, giving you total control over your documents.
Conclusion
Persistent Protection After Download (PPAD) represents a breakthrough in document security. Whether you’re a business, educator, or content creator, PPAD ensures your files remain protected, traceable, and under your control, even after download. Say goodbye to lost control, unauthorized redistribution, and compliance risks. With VeryPDF DRM Protector, your security travels with your files, no matter where they go.
Take full control of your digital content today with Persistent Protection After Download (PPAD), because once your file leaves your system, you should still stay in charge.